By Adrian | November 4, 2019
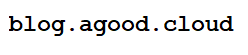
When it comes to your website, whats better than an A on your Qualys report? Why it has to be that A+! It might not seem like a big deal, but I still wanted to max out my score where I could. Little did I know I was about to get an education in the process. The Qualys SSL labs tester can be accessed via this URL https://www.ssllabs.com/ssltest/analyze.html. My initial report came back as follows:
The recommendations I could see from my report was that I didn’t have a Certification Authority Authorization (CAA) DNS record and that I was still allowing TLS 1.1 connections. Left unchecked, my A grade would slip to a B grade in January 2020. Can’t have that now can we?
Lack of CAA Record in DNS
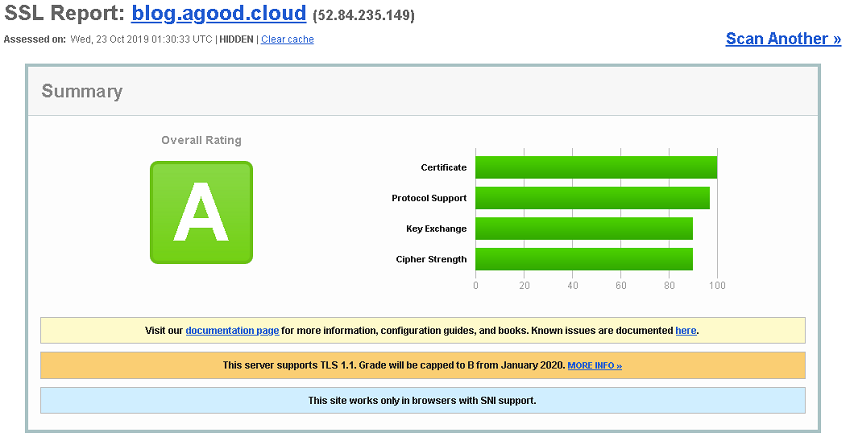
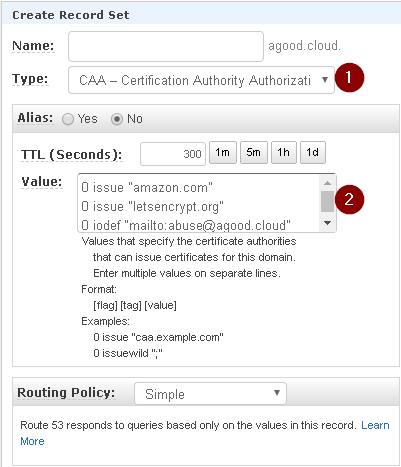
The CAA record in a nutshell says which certificate authorities are allowed to issue certificates for my domain. Well that was going to be an easy one to knock over given that I only us Amazon and Let’s Encrypt for my certificates (yay for free certs). To create the CAA DNS record, I headed over to the SSLMate CAA record generator website where its just a matter of plugging in your website, selecting the Authoriszed Certificate Authorities, adding an incident reporting address and collecting the resulting output (below).
0 issue "amazon.com"
0 issue "letsencrypt.org"
0 iodef "mailto:abuse@agood.cloud"
With the following policy in my clipboard, I logged into AWS, went to Route53, selected my Hosted Zone and pressed Create Record Set. Next I selected the CAA - Certification Authority Authorization Type and pasted in the Value. Pressed Create and waited a few moments.
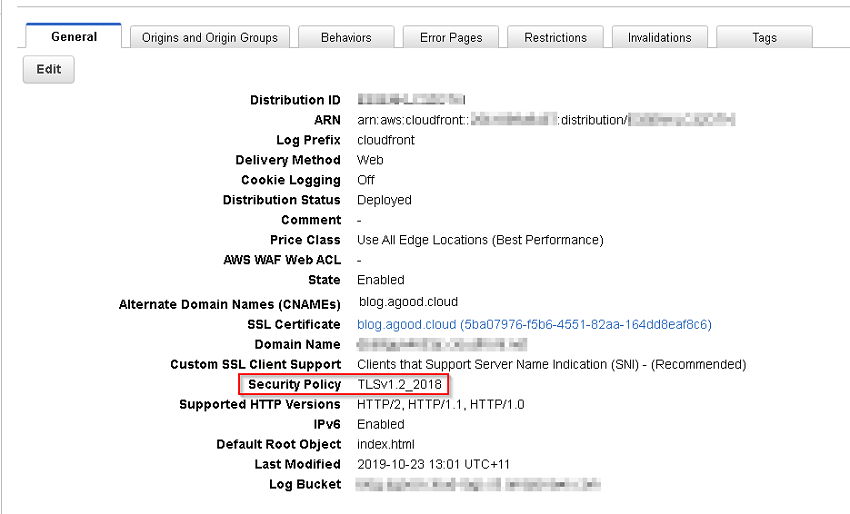
Remove TLS 1.1
Removing TLS1.1 was also just a matter of flicking a setting over in CloudFront, selecting the appropriate Distribution, pressing Edit (on the general tab), and changing the Security Policy to TLSv1.2_2018. Then waiting for the changes to propogate through CloudFront which takes about 15-20 minutes.
Lets get that A+ honour badge
Sweet, with those 2 points covered off, it was back to the Qualys test to pickup that honor badge.
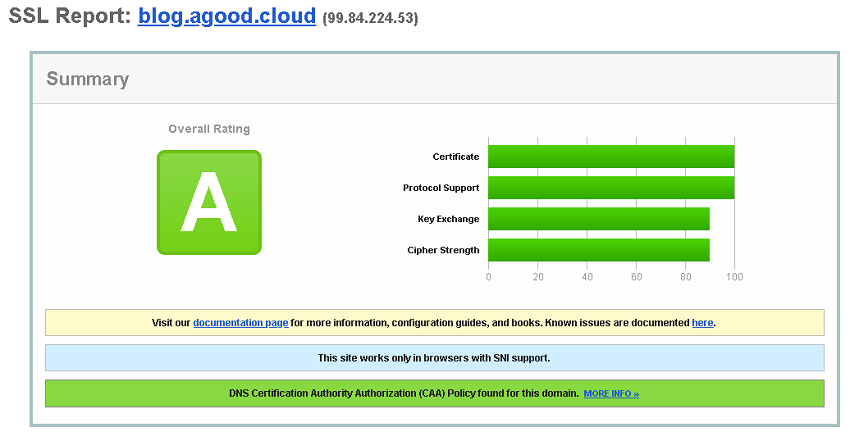
What the? My rating literally didn’t budge at all! Further down in the actual report there was mention that Strict Transport Security (HSTS) wasn’t enabled. This is where things took an interesting turn which you will see in the next post. Stay tuned.