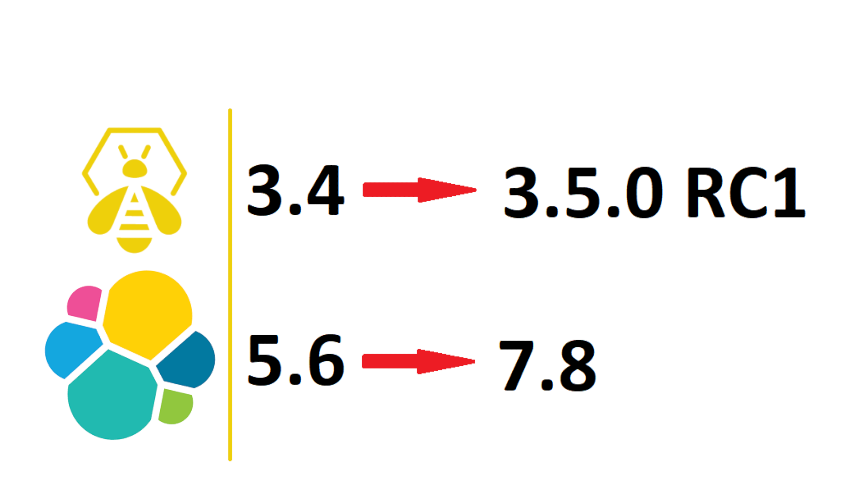
Upgrading TheHive 3.4.0-1/ES5.6 to TheHive 3.5.0-RC1/ES7.8
TheHive 3.5.0 RC1 has now been released and my environment is in a bit of a shambles for this upgrade. You see when I performed my upgrade of TheHive 3.2.1 to 3.4.0 I elected to not upgrade to ElasticSearch 6.8 at the time as I wanted to do some more testing on it. I told myself, TheHive 3.4 was working just fine using Elasticsearch 5.6, so I never went ahead with the Elastic part of the upgrade.